Goodbye SSH Brute-force!

Principal Research & Translation Specialist at ST Engineering Info-Security Pte Ltd
TL;DR
- Sign-up https://zerotier.com, free for the 1st 50 devices!
- Create a Zerotier private network
- Join private network, both ssh-server & client
- Configure
sshdto listen with private IP - Goodbye ssh-brute-force!
Why?
Reduce Attack-Surface
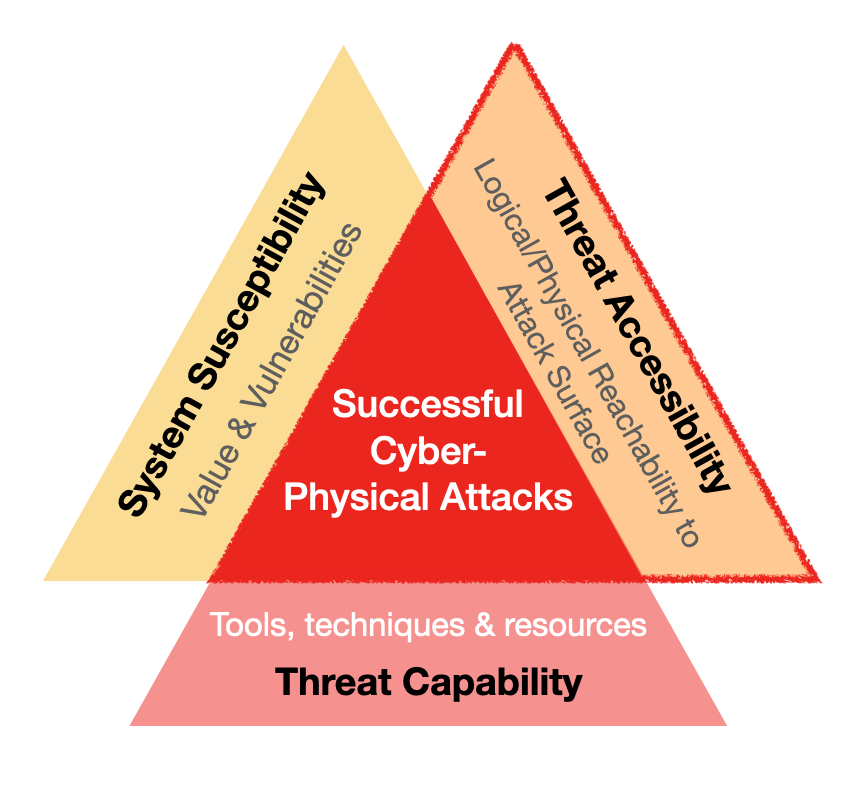
When we disrupt one or more of the Necessary & Sufficient conditions for any Cyber-Physical attacks, in this case Threat Accessibility, we lower the risk ( probability). This applies to other administrative service/ports.
Even if there were a 0-day ssh-server vulnerability that is exploitable, attackers will need to first get into your client.
Enabling Multi-Factor/Step Authentication on your VPS provider is also related to Threat Accessibility.
Improve "Signal-to-Noise" Ratio
Server-logs are useful for investigating any incidents. When cluttered with blocked/refused SSH attempts, those entries are simply "noise", which will be eliminated after this configuration.
Storage is Precious
Why waste it on "noise"?